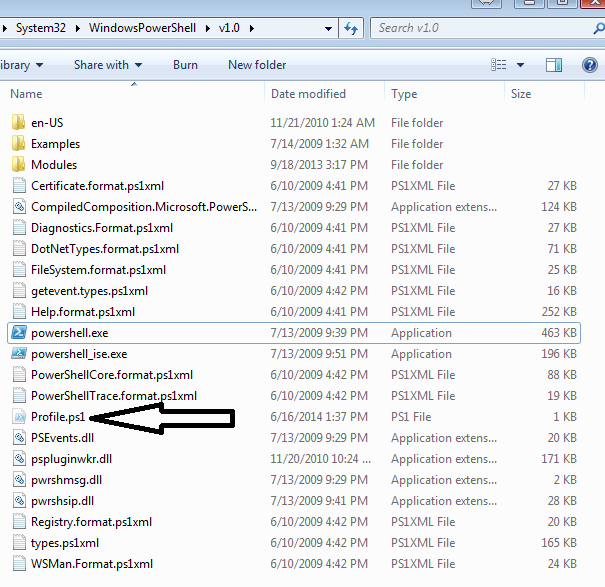
Working in IT, I see a lot of guys use Powershell profiles to customize their shell so they don’t have to do it each time. I found this interesting and decided to look into it a little further. In a nutshell, you can create any automatic customization you need and save it in profile.ps1 in the $PsHome directory (C:\Windows\System32\WindowsPowershell\v1.0\). If that file exists, it executes the contents when powershell.exe is executed. This is Microsoft’s attempt to make the Powershell console easy to customize.
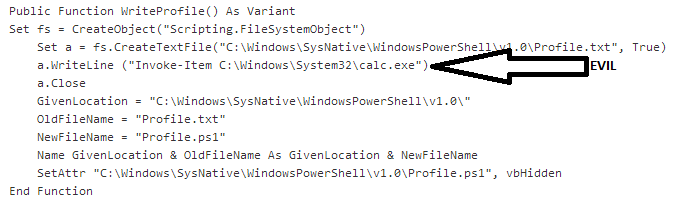
This can also be used for malicious purposes. For example, an attacker can create or override profile.ps1 with malicious code and force powershell.exe to execute in the background. I crafted a malicious excel document that takes advantage of this.
The macro for this can be found on my Github here:
https://github.com/enigma0x3/PowershellProfile
The workflow goes like this: The document is opened and the macro is executed. Upon execution, the macro creates a file called “cookie.txt” in C:\Users\Default\AppData\Roaming\Microsoft\Cookies\. Once created, it writes a wrapper that executes powershell.exe silently, changes the extension from .txt to .vbs and then sets the file attributes to “hidden”. It is important to note that the “Default” user profile is hidden by default, along with the “Cookies” folder within that profile.
It is just a vbs wrapper that executes Powershell and hides everything from the user. With cookie.vbs (containing a silent powershell launcher) created, it creates a new profile ps1 in C:\Windows\System32\WindowsPowershell\v1.0\. One thing to note is the macro sets the path as C:\Windows\SysNative instead of C:\Windows\System32 in order to bypass Microsoft’s File System Redirector. This is the malicious part. My example just uses Powershell to execute calc.exe, but you can put any malicious Powershell script in there. Another thing to note is that it sets the attributes of Profile.ps1 to hidden as well.
As many of you know, the code in profile.ps1 will execute when Powershell is launched. At this point, we have malicious code in profile.ps1 and a vbscript that executes Powershell silently. The last part of this attack is the persistence portion. The malicious macro then creates a registry key in HKCU:\Software\Microsoft\Windows NT\CurrentVersion\Windows\Load and points it to cookie.vbs in the Default profile.
When the user logs in, the registry key executes cookie.vbs which executes Powershell.exe silently. Because we have calc.exe (or malicious code) in Profile.ps1, it is executed as well….silently of course.
-Matt Nelson (@enigma0x3)



marvelous pure awesomeness